
When an unfamiliar dependency such as bvostfus python appears in a build, installer, or repo, treat it as an untrusted supply-chain input until you can prove what it is, where it came from, and how it behaves at runtime. This guide shows a verification-first way to install, troubleshoot, and remediate issues tied to bvostfus python.
- Why unknown dependency names are a security risk
- Pre-install verification (quick and objective)
- Secure installation patterns (pin + constrain + verify)
- Issue-first troubleshooting (fix the class of failure)
- Logs and evidence (collect before changing more)
- Foxtpax: validate separately
- Remediation loop (repeatable playbook)
- Pros and cons
- Conclusion
Why unknown dependency names are a security risk
In Python, unexpected names can come from typosquatting, dependency confusion, or bundled installers. If bvostfus python is not documented by your project owner or organization, pause and verify. If you’re new to python basics, remember: “it installed” is not proof of safety.
Pre-install verification (quick and objective)
Before you install bvostfus python, capture evidence you can audit:
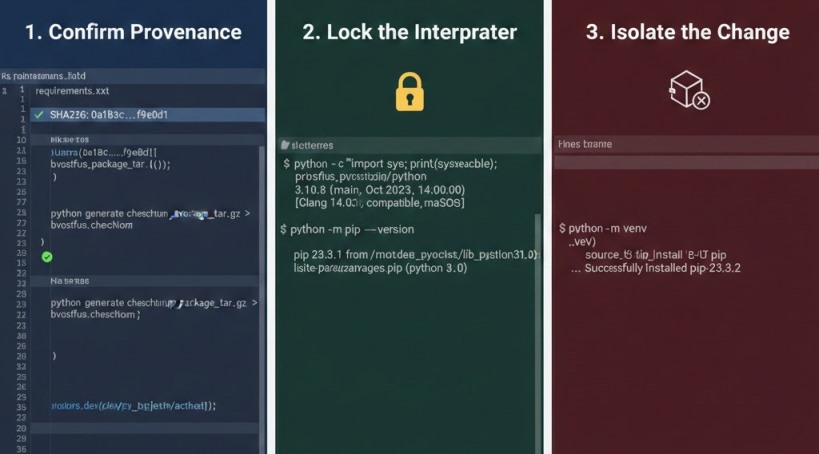
A) Confirm provenance
Record the exact source and approved version. If you received an artifact file, compute and store its checksum.
B) Lock the interpreter
Many failures happen because pip installs into one interpreter while the app runs another:
python -c "import sys; print(sys.executable); print(sys.version)"
python -m pip --version
C) Isolate the change
Install only inside a fresh virtual environment:
python -m venv .venv
python -m pip install -U pip
If bvostfus python breaks dependencies, delete the venv.
Secure installation patterns (pin + constrain + verify)

If policy requires you to install bvostfus python, use controls that prevent drift:
A) Pin what you install
Use an exact, approved version (avoid floating specs).
B) Hash-checking when available
If hashes are provided, enforce them so pip refuses altered artifacts:
python -m pip install --require-hashes -r requirements.txt
C) Constrain transitive dependencies
Use constraints.txt so upgrades can’t surprise you:
python -m pip install -r requirements.txt -c constraints.txt
D) Capture an install record
python -m pip install --report install-report.json <approved-source>
python -m pip check
This helps incident review and faster bvostfus python issue fix work.
Issue-first troubleshooting (fix the class of failure)
Avoid “random commands.” Identify the failure category and fix systematically.
A) Import/path errors
Symptoms: ModuleNotFoundError, missing CLI entry points, or wrong package at runtime. Fix by confirming the venv is active and printing import paths:
python -c "import sys; print('\n'.join(sys.path))"
If bvostfus python was installed outside the venv, rebuild it.
B) Resolver conflicts
Symptoms: pip warnings, crashes after installs, or incompatible versions. Fix by reinstalling from pinned files and validating with pip check. Save a known-good snapshot:
python -m pip freeze > requirements-lock.txt
C) Native build failures
Symptoms: compiler errors, missing headers, wheels unavailable for your platform. Prefer prebuilt wheels from trusted sources; otherwise align build tools to your Python version. This is common with psycopg2.
Also Read: Software Dowsstrike2045 Python: Next-Gen Framework Power!
Logs and evidence (collect before changing more)
Good logs beat guesswork—especially with bvostfus python.
A) pip logs
python -m pip install -v <approved-source> 2>&1 | tee pip-install.log
python -m pip debug -v > pip-debug.txt
B) Application logs
Use logging to capture stack traces and relevant context. If the dependency reads environment files (for example python-dotenv), log missing keys without printing secrets.
C) Security telemetry
If bvostfus python arrived via a nonstandard installer, include endpoint alerts and process history.
Foxtpax: validate separately
If Foxtpax appears alongside bvostfus python, treat it as a separate trust decision. Ask for vendor identity, version, distribution method, and chain of custody. Collect information about foxtpax software from authoritative internal records or signed vendor documentation. If you cannot obtain trustworthy information about foxtpax software, test in a VM and avoid admin rights by default.
Remediation loop (repeatable playbook)
For a stable environment impacted by bvostfus python, use this loop:
1. Reproduce once and save logs
2. Confirm interpreter/venv
3. Rebuild venv from pinned files
4. Run pip check
5. Re-test with debug logging.
That disciplined cycle is the bvostfus python issue fix that scales.
Pros and cons
Pros: reduces supply-chain exposure, makes rollback easy, improves incident response quality.
Cons: requires pinned files and a bit more process up front.
Conclusion
Treat bvostfus python as an untrusted dependency until you verify provenance, integrity, and runtime behavior. Install only in isolated environments, pin and constrain versions, and capture pip plus OS logs before changing anything. A repeatable, evidence-driven workflow prevents dependency confusion, speeds fixes, and strengthens incident response.