
Thejavasea.me leaks aio-tlp370 is best understood as an online leak-related label, not an official security standard. The safe response is immediate: verify exposure, rotate credentials, enable multifactor authentication, and check for leaked secrets. Searchers want clear meaning, real risks, and practical fixes. This article provides all three clearly.
What Thejavasea.me leaks aio-tlp370 actually means
Current pages using this keyword generally describe it as a leak package or bundled dump label attached to data, tools, or files circulating through leak channels. That explains the search demand, but it does not make the label official or trustworthy.
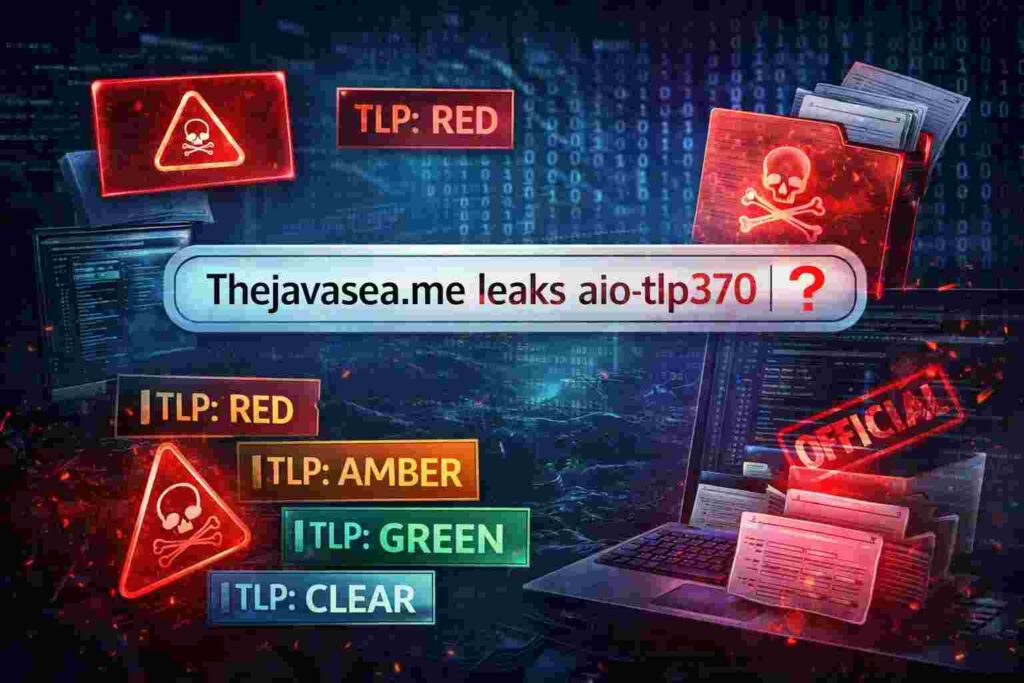
That distinction matters because TLP370 sounds technical enough to be confused with the Traffic Light Protocol used in cybersecurity. Under the official FIRST standard, the valid labels are TLP:RED, TLP:AMBER, TLP:GREEN, and TLP:CLEAR. There is no official TLP370 designation.
So the keyword should be read as a search phrase tied to an alleged leak, not as a recognized incident classification. That is the first correction many competing articles miss, and it is the reason searchers often leave the SERP without getting a reliable answer.
Why this term creates real security concern

Whether every claim around the package is true or not, the risk pattern is familiar. If a leak bundle contains credentials, tokens, source code, configuration files, or operational notes, attackers gain both direct access opportunities and a roadmap for further abuse. GitHub’s official secret scanning guidance specifically covers exposure of API keys, passwords, tokens, and other secret types, which shows how common and serious this problem is.
The first danger is credential reuse. Once a password or login pair is exposed, attackers test it across email, hosting, admin panels, cloud services, and shared tools. OWASP recommends credential rotation when a password leak occurs, which is exactly the right response here.
The second danger is exposed secrets. Hardcoded API keys, environment variables, and deployment tokens can open live services even when passwords look secure. OWASP’s secrets management guidance stresses that secrets must be stored, audited, and rotated in a controlled way because compromised secrets can quickly turn into system compromise.
The third danger is follow-on phishing and impersonation. Once a leak gets attention, fake login prompts, urgent warning emails, and malware attachments usually follow. CISA states that multifactor authentication significantly reduces the risk of account compromise and urges organizations to move toward phishing-resistant MFA where possible.
Risks, meaning, and fixes at a glance
| Area | What it means | Main risk | Best fix |
|---|---|---|---|
| Keyword meaning | Leak-related label, not an official TLP code | Misreading the issue and delaying action | Treat it as an exposure warning, not a standard |
| Credentials | Usernames, emails, passwords, session data | Account takeover and credential stuffing | Reset passwords, revoke sessions, enable MFA |
| Secrets | API keys, tokens, config values, environment data | Service abuse and backend access | Rotate keys, audit repos, reduce permissions |
| Code and docs | Source code, notes, internal references | Faster exploitation and recon | Patch exposed weaknesses and review logs |
This is the practical lens you should use. Do not get distracted by the label itself. Focus on what could be exposed, how attackers would use it, and which controls stop damage fastest.
What to do if you may be affected
Start with exposure checking. Use Have I Been Pwned to see whether an email address appears in known breach data. The service also offers notifications when your email shows up in future breaches, which makes it a useful early-warning layer.
Then move to credential containment. Change passwords anywhere reuse is possible, force sign-outs on important accounts, and turn on MFA everywhere it matters. CISA is clear on this point: MFA is a simple, effective control that blocks many common attacks and reduces account compromise risk.
Next, review for secret leakage. Search repositories, CI/CD settings, deployment files, and environment records for access tokens, cloud keys, webhook secrets, database strings, and admin credentials. GitHub’s documentation is explicit that secret scanning exists to detect exactly these accidental exposures across repository history.
After that, harden the accounts that matter most. Phishing-resistant MFA such as FIDO/WebAuthn or security keys gives much better protection than weaker methods when attackers try to steal sessions through fake login pages. CISA’s phishing-resistant MFA guidance makes that hierarchy clear.
Finally, watch for secondary abuse. Monitor login alerts, billing changes, forwarding rules, new OAuth grants, unusual API usage, and suspicious password reset requests. A leak rarely stays isolated. The real damage often starts after the first round of public attention.
Why most content on this keyword falls short
Most articles targeting this phrase recycle the same structure: a vague definition, a broad warning, and generic advice. That leaves a gap in the one place users actually need help, which is verification.
The stronger approach is to explain that TLP370 is not an official cybersecurity label, then move straight into response priorities: check exposure, rotate credentials, scan for secrets, and harden authentication. That adds real information gain and gives the page a reason to rank beyond keyword repetition.
FAQs
What is Thejavasea.me leaks aio-tlp370?
It is generally used online as a leak-related label, not a formal cybersecurity standard.
Is TLP370 an official Traffic Light Protocol code?
No. Official FIRST labels are TLP:RED, TLP:AMBER, TLP:GREEN, and TLP:CLEAR.
What is the biggest risk here?
The biggest practical risks are credential reuse, exposed secrets, and phishing after publicity spreads.
What should I do first?
Check breach exposure, rotate passwords and keys, enable MFA, and review systems for exposed tokens or config secrets.
Treat Thejavasea.me leaks aio-tlp370 as a potential exposure signal, not a trusted technical classification. The right fix is disciplined action: verify accounts, rotate passwords and secrets, enforce stronger MFA, scan repositories, and monitor for abuse. That response limits damage, protects systems, and turns a vague keyword into a concrete security decision framework.